DATA(service_manager) = NEW cl_hrpp_ws_service_manager( ).
SELECT * INTO TABLE @DATA(lt_t52el) FROM t52el WHERE molga = '01' AND symko <> @space AND endda >= @pn-begps. " Verknüpfung Lohnart zu symbolischen Konto
SELECT * INTO TABLE @DATA(lt_t52ek) FROM t52ek. " Symbolische Konten
SELECT * INTO TABLE @DATA(lt_t52ep) FROM t52ep. " Kontierungsarten
LOOP AT lt_t52el INTO DATA(ls_t52el). " Ermittle je Lohnart die symbolischen Konten (1:n)
TRY.
DATA(ls_t52ek) = lt_t52ek[ symko = ls_t52el-symko ]. " Ermittele Kontierungsart
DATA(ls_t52ep) = lt_t52ep[ koart = ls_t52ek-koart ]. " Ermittele Typ des symbolischen Kontos
DATA(process) = CONV ktosl( 'HR' && ls_t52ep-kttyp ).
CATCH cx_sy_itab_line_not_found.
CONTINUE.
ENDTRY.
service_manager->hrpp_fi_acct_det_hr( EXPORTING companycode = pernr-bukrs
process = process " Vorgangsschlüssel
symb_acct = ls_t52el-symko
eg_acct_det = CONV #( '1' ) " Überleitung FI/CO: Mitarbeitergruppierung Kontenfindung: alle Mitarbeiter
IMPORTING gl_account_debit = DATA(account_debit)
gl_account_credit = DATA(account_credit)
return_tab = DATA(return_tab) ).
IF line_exists( return_tab[ type = 'E' ] ).
CONTINUE.
ENDIF.
" Lese Sachkonto Text
service_manager->hrpp_gl_acc_getdetail( EXPORTING companycode = pernr-bukrs
glacct = account_debit
language = sy-langu
text_only = abap_true
IMPORTING account_detail = DATA(account_detail) ).
ENDLOOP.
Tag: SAP
[Fiori] Display MyInbox content of a specific user
You can use the SAP_WAPI_CREATE_WORKLIST function module to display all workitems that are currently in a user’s inbox. This is very useful, as you cannot use the “on behalf of” function in MyInbox.
[SAP] System upgrade – Find related notes
Brief overview of how to find all notes contained in the installed SPs during a system patch.
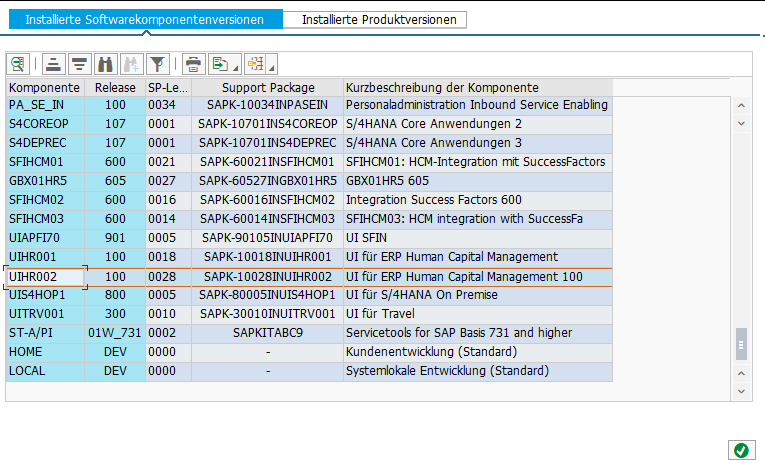
First, look up the new SP level for a specific component. For example, if the old SP level was 0026 and the patch it is 0028, you need to check the notes for SP 0027 and 0028.
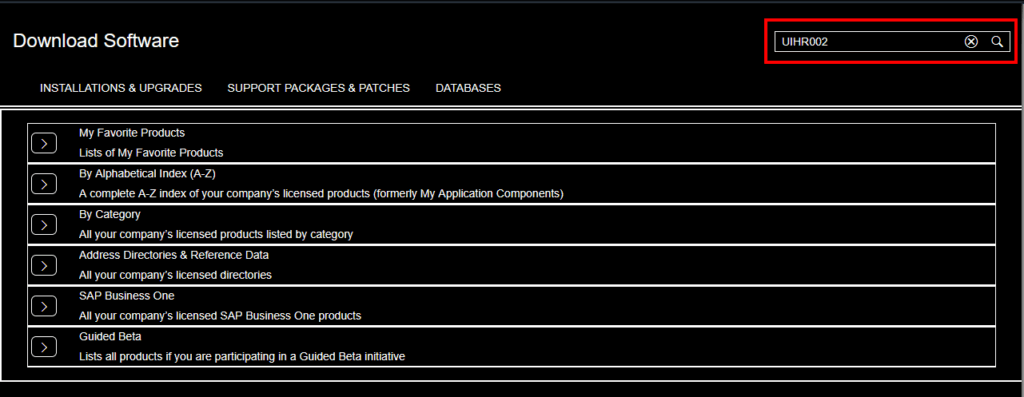
Then open the SAP Software center: https://me.sap.com/softwarecenter (or via https://support.sap.com/en/index.html and click on Software Downloads)
Search for component UIHR002
Click on “Maintenance Software Component”
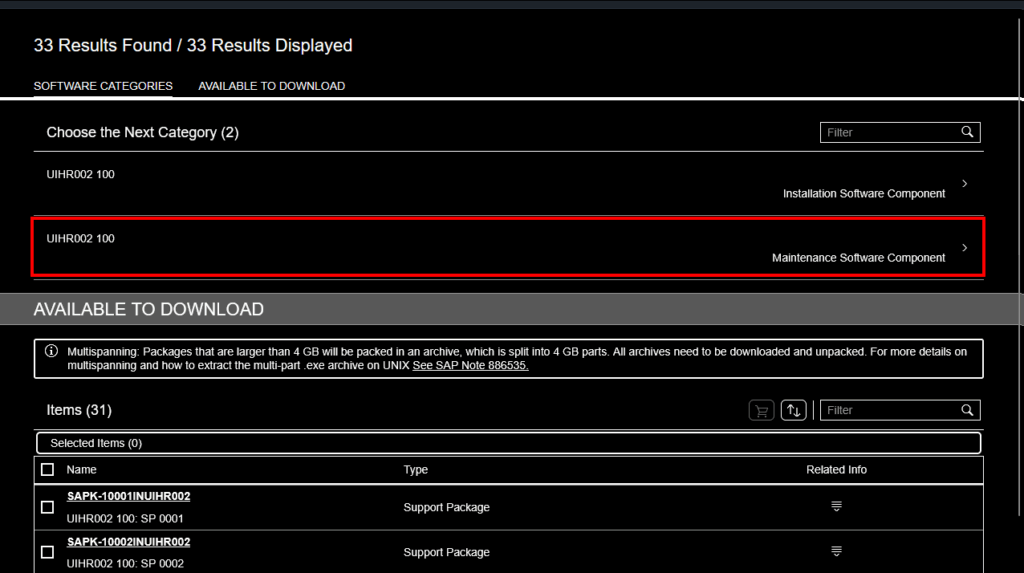
Click on “SUPPORT PACKAGES”
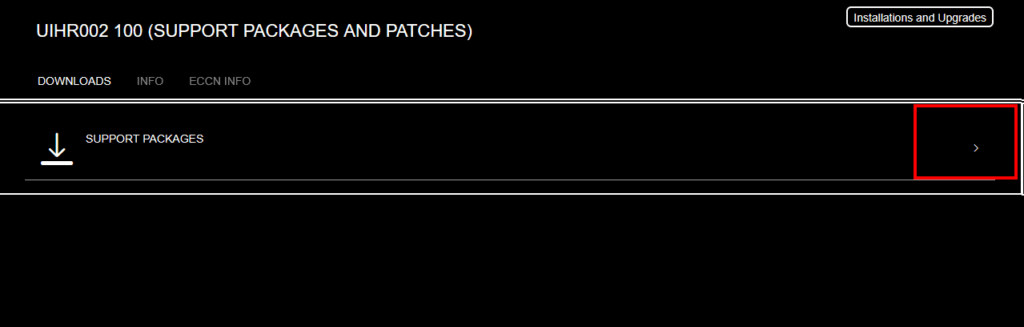
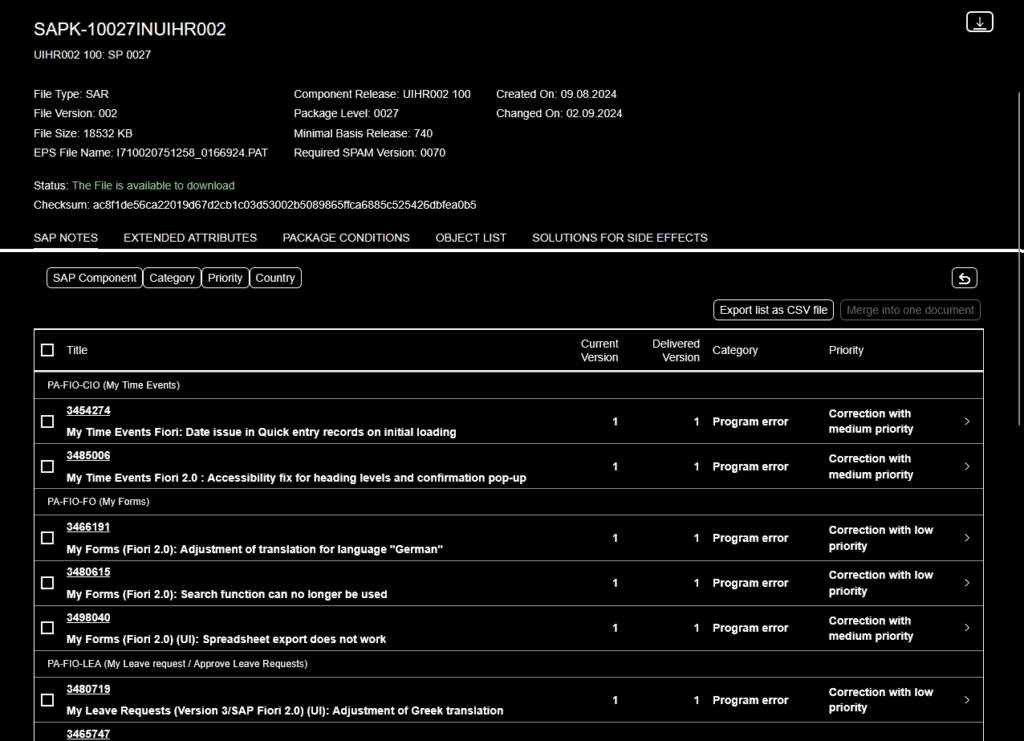
Choose a package you want to view the notes for and click on “Content Info”
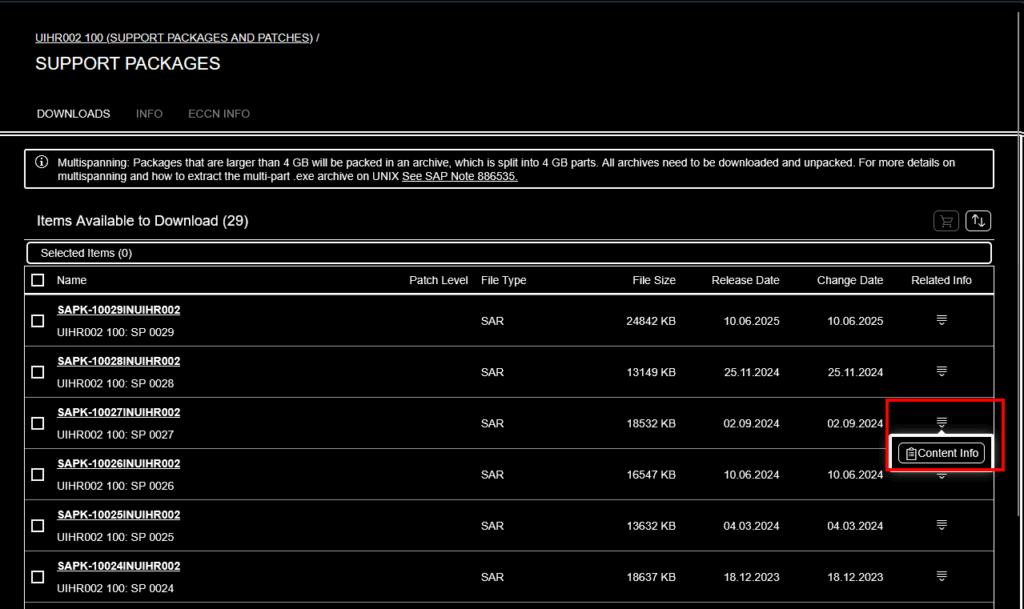
Now it will list all notes which are included
[SAP] Initiale Dinge, die ich für jeden neuen SAP Gui Zugang erledige
Das System in KeePass hinzufügen, für die 1-Klick Anmeldung.
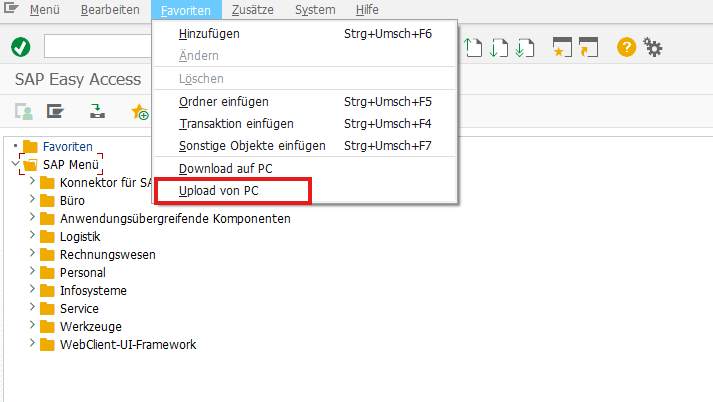
Meine Favoriten importieren. (Man kann übrigens einfach Favoriten über das Kommandofeld hinzufügen via %_GCADDF, technisch liegen die Favoriten in der Tabelle SMEN_BUFFC). Reference OSS note 456728 – Easy Access: download/upload of favorites.
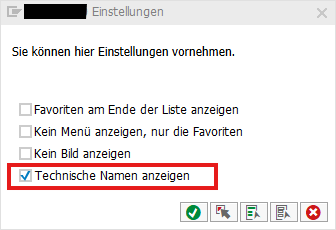
Unter Zusätze → Einstellungen (Umschalt + F9) die Einstellungen öffnen und “Technische Namen anzeigen” anhaken
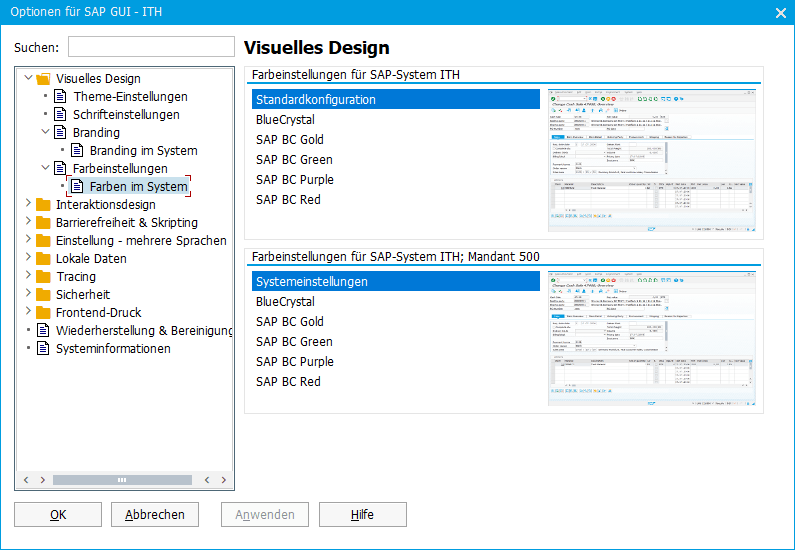
Unter Optionen das Theme von Belize auf Blue Crystal abändern und eine Systemfarbe einstellen
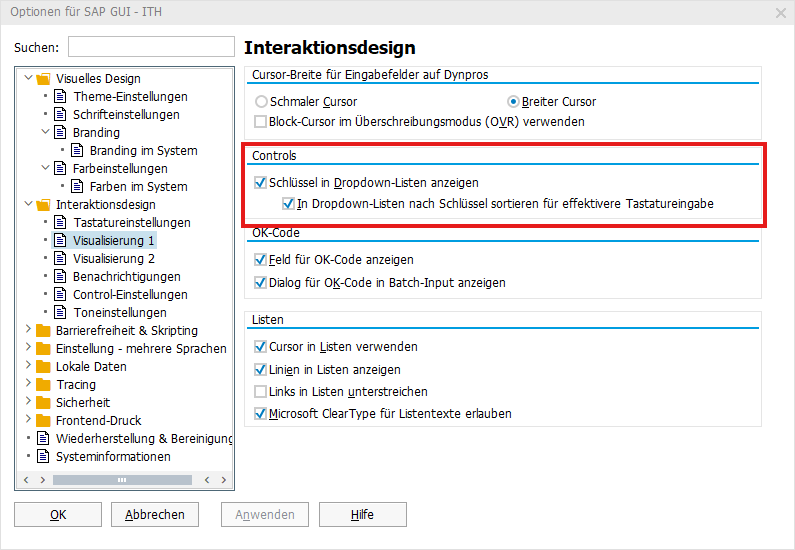
sowie Schlüssel in Dropdown-Listen anzeigen
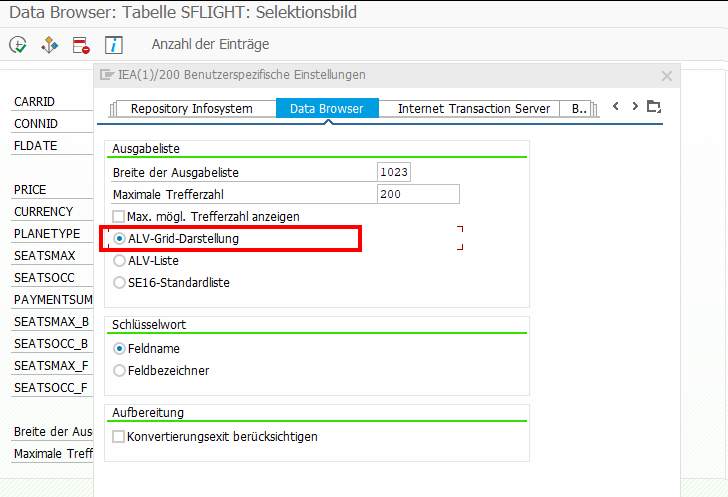
In der SE11 über Hilfsmittel → Benutzerdefinierte Einstellungen → Data Browser → Ausgabenliste die ALV-Grid-Darstellung aktivieren
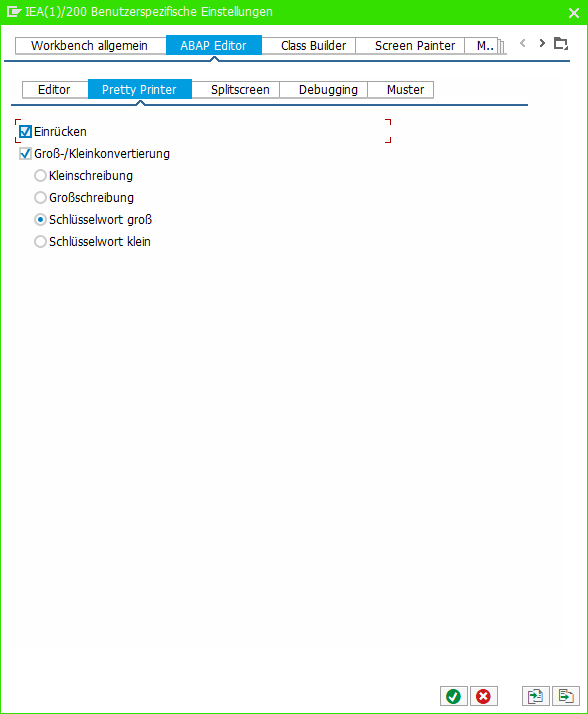
In der SE80 über Hilfsmittel → ABAP Editor → Pretty Printer die folgenden Einstellungen setzen
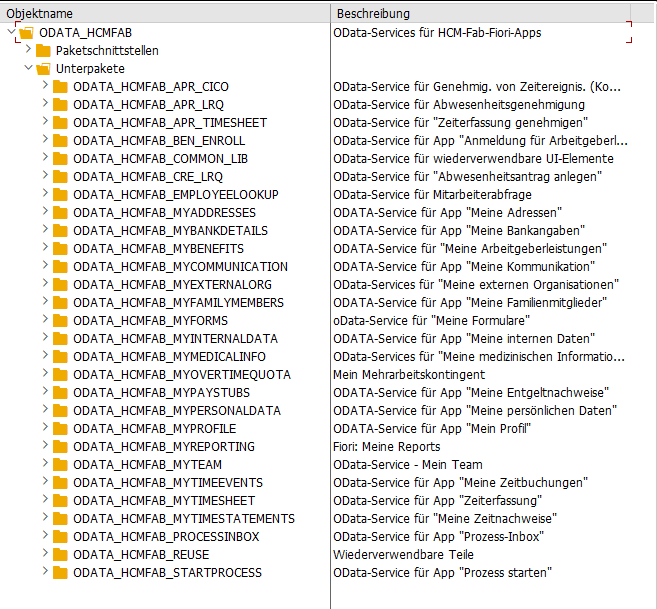
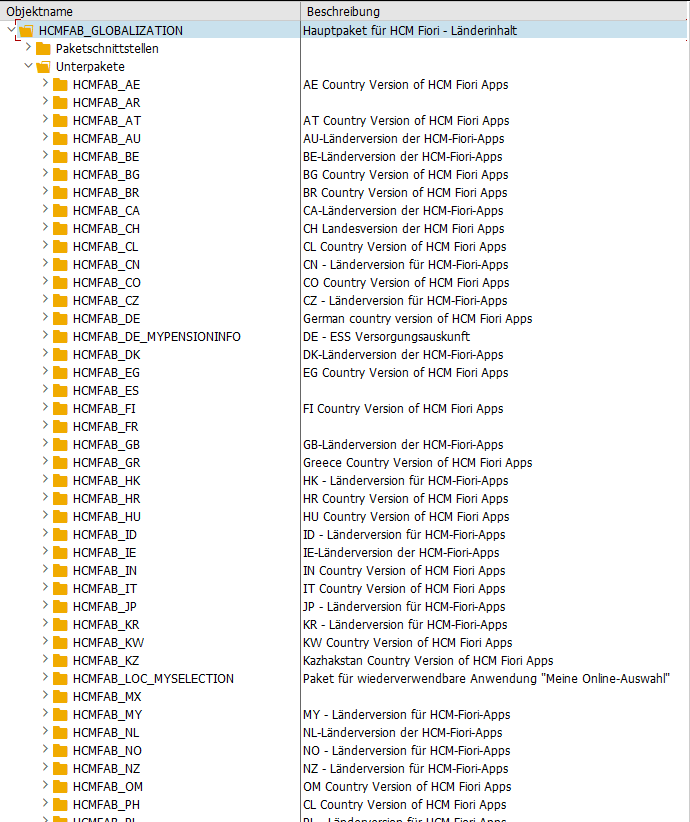
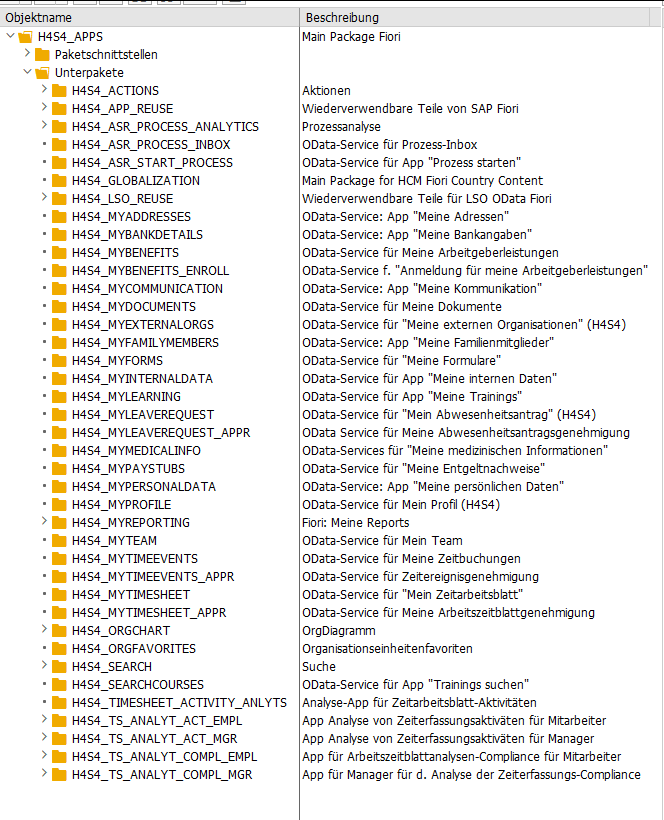
[Fiori] HCM Fiori Apps: Frontend & Backend Pakete
Fiori 2.0 Apps in SAP Human Capital Management
Frontend: CONTENT_HCM_APPS
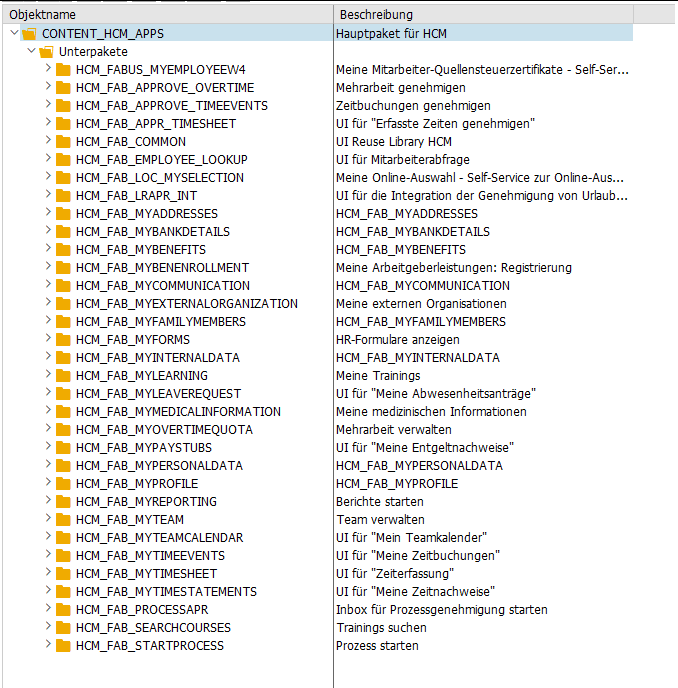
Backend: ODATA_HCMFAB
Backend: HCMFAB_GLOBALIZATION
Länderspezifische Logik findet man in diesen Paketen, wie z.B. MyForms Implementierungen.
Fiori Apps in SAP Human Capital Management for SAP S/4HANA
Frontend: CONTENT_HCMS4_APPS
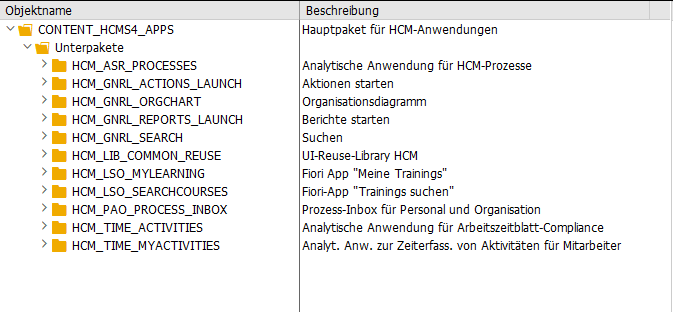
Backend: H4S4_APPS
Allerdings sind auf Releasestand H4S4 2022 SP05 die meisten Pakete noch leer.
[ABAP] Enqueue and dequeue pernr
TRY.
DATA(messsage_handler) = NEW cl_hrpa_message_list( ).
cl_hrpa_masterdata_enq_deq=>enqueue_by_pernr( tclas = cl_hrpa_tclas=>tclas_employee
pernr = 1
message_handler = messsage_handler ).
cl_hrpa_masterdata_enq_deq=>dequeue_by_pernr( tclas = cl_hrpa_tclas=>tclas_employee
pernr = 1 ).
CATCH cx_hrpa_violated_assertion.
ENDTRY.
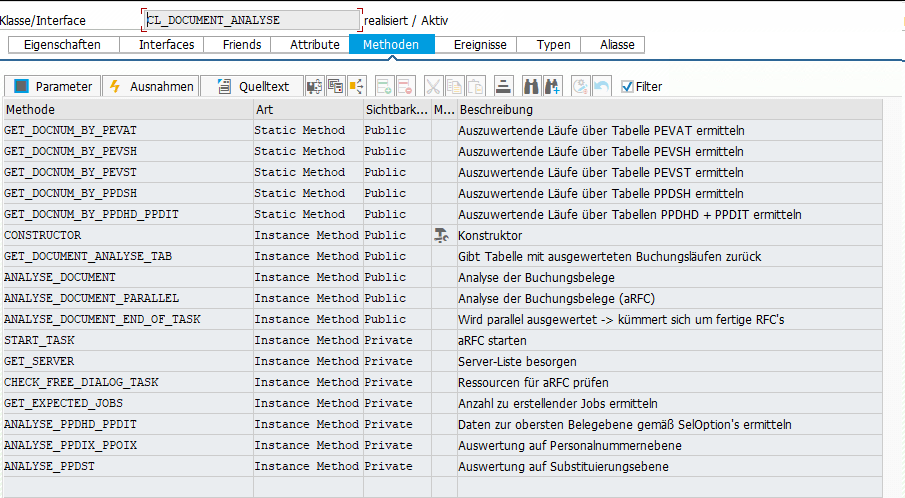
[HR] Buchungsbelege anzeigen/analysieren
Hilfreiche Reports:
- SAPMPCP0 – Buchungsläufe bearbeiten (TCode PCP0)
- H99CWTR0 – Lohnarten Reporter
- RPCIP_DOCUMENT_ANALYSE – Buchungsbelege analysieren
- RPCIPD00_FRAME – Details zu Belegzeilen anzeigen
Einige relevante Tabellen:
- PPDHD – Überleitung FI/CO: Kopf des Belegs
- PPDIT – Überleitung FI/CO: Zeilen des HR-Zwischenbelegs
- PPDIX – Überleitung FI/CO: Indextabelle der HR-Zwischenbelege (Verknüpfung zwischen PPDIT und PPOIX)
- PPDST – Überleitung FI/CO: Substituierte Kontierungsobjekte
- PPOIX – Index Abrechnungsergebniszeile -> Buchungszeile
- PPOPX – Index alte <-> neue Belegzeile für ‘P’-Ergebnisse
- PEVST – Abrechnungsauswertungsläufe
- PEVAT – Attribute von Auswertungsläufen
- PEVSH – Historie von Abrechnungsauswertungsläufen (STATUS = 40 Überleitung an FI)
Die Klasse CL_DOCUMENT_ANALYSE hilft die Verknüpfung der Tabellen zu verstehen
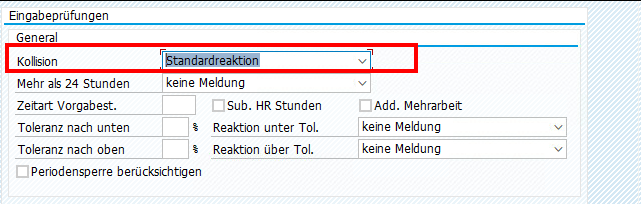
[HR] Zeiterfassung: Kollisionsprüfung aktivieren
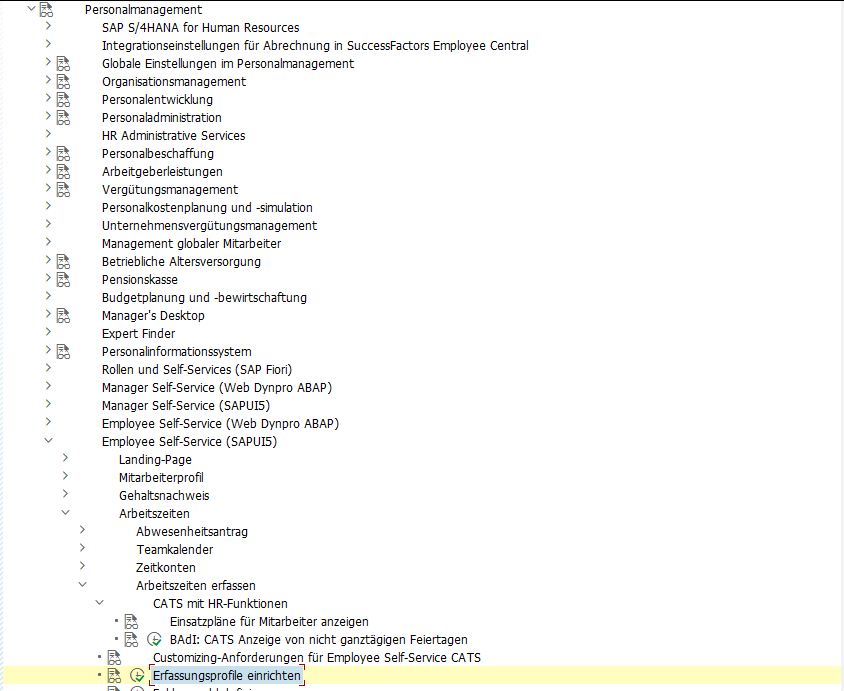
SPRO → Personalmanagement → Employee-Self-Service (SAPUI5) → Arbeitszeiten → Arbeitszeiten erfassen → Erfassungsprofile einrichten